How to create a security group with Inbound & Outbound rules in AWS EC2 Instance
To create security group with Inbound & Outbound rules in AWS EC2 Instance
Introduction:
A security group runs as a virtual firewall for the EC2 instances to regulate incoming and outgoing traffic. If we didn't define a security group, Amazon EC2 utilizes the default security group which can add rules to each security group and allows traffic to or from its associated instances.
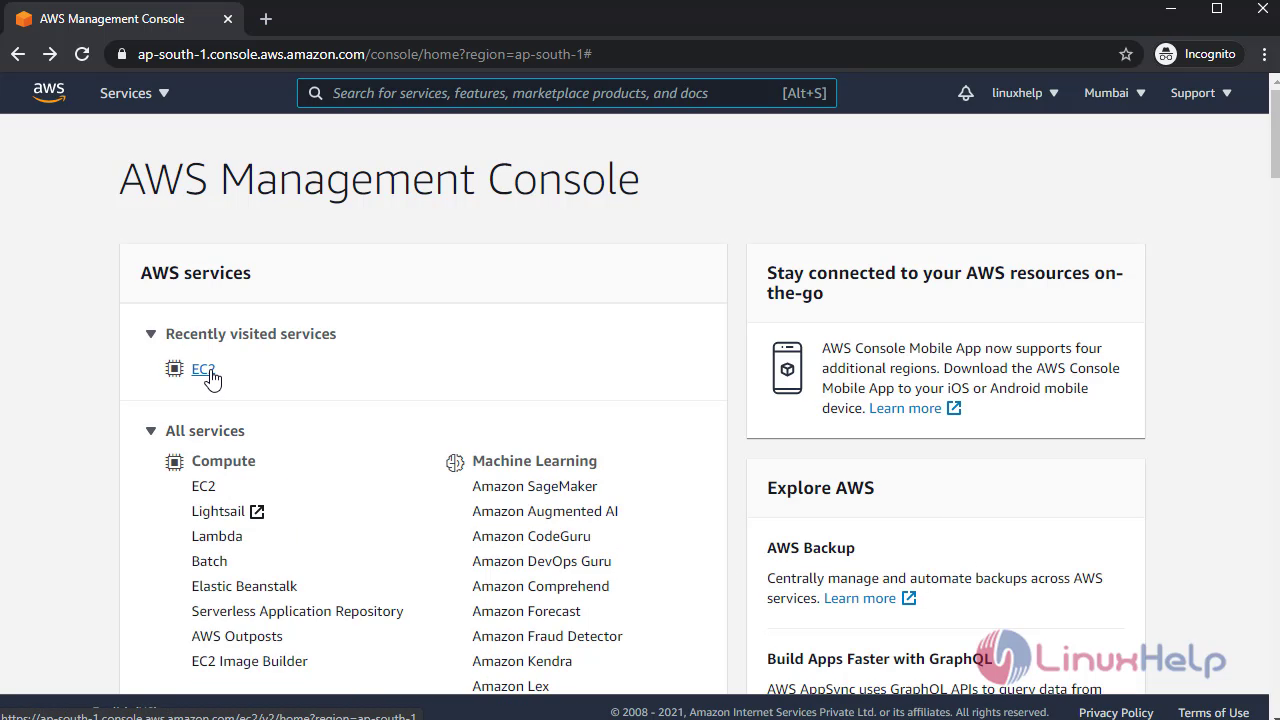
Login to your AWS account:
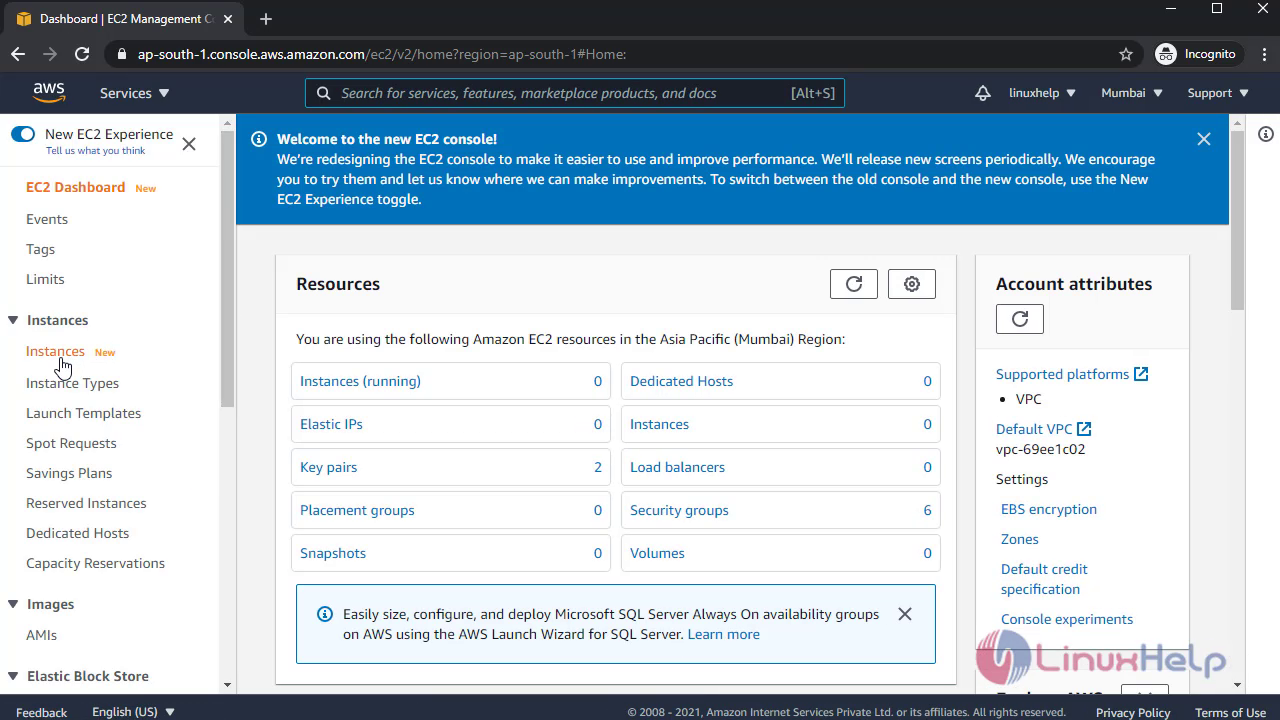
In AWS Console management click EC2 services:
 Then click Instances to Launch Instances:
Then click Instances to Launch Instances:
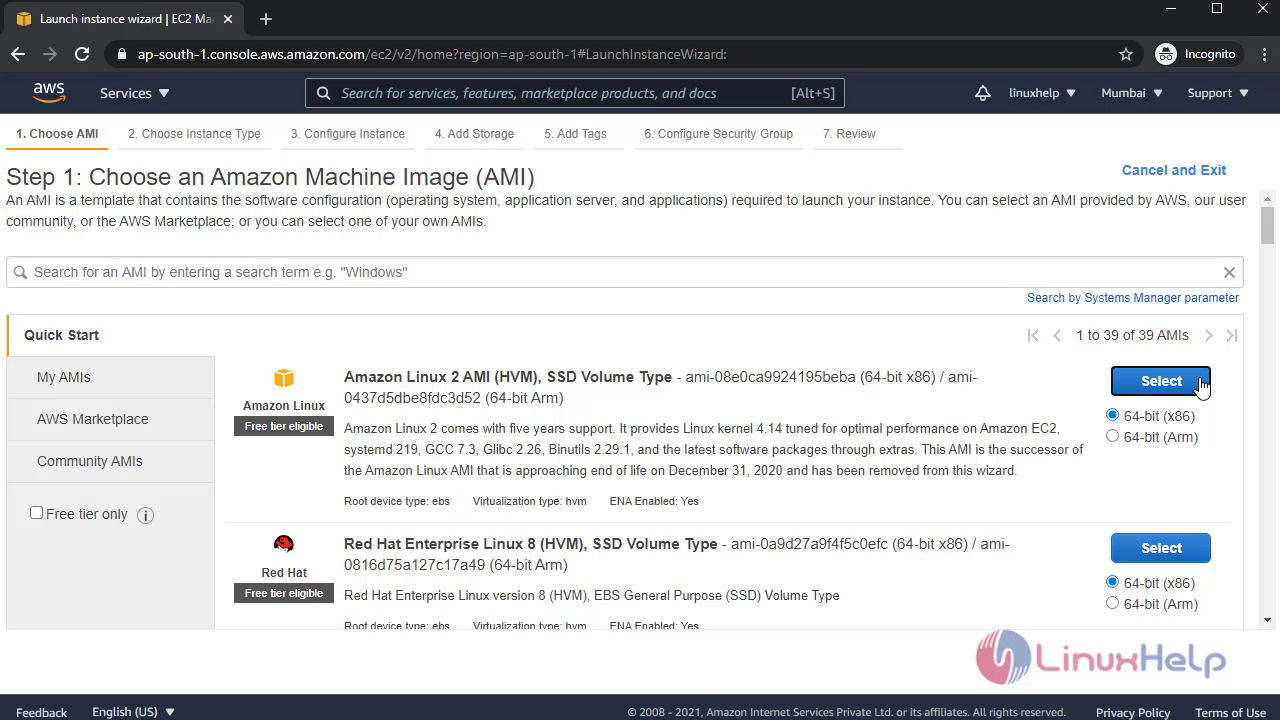
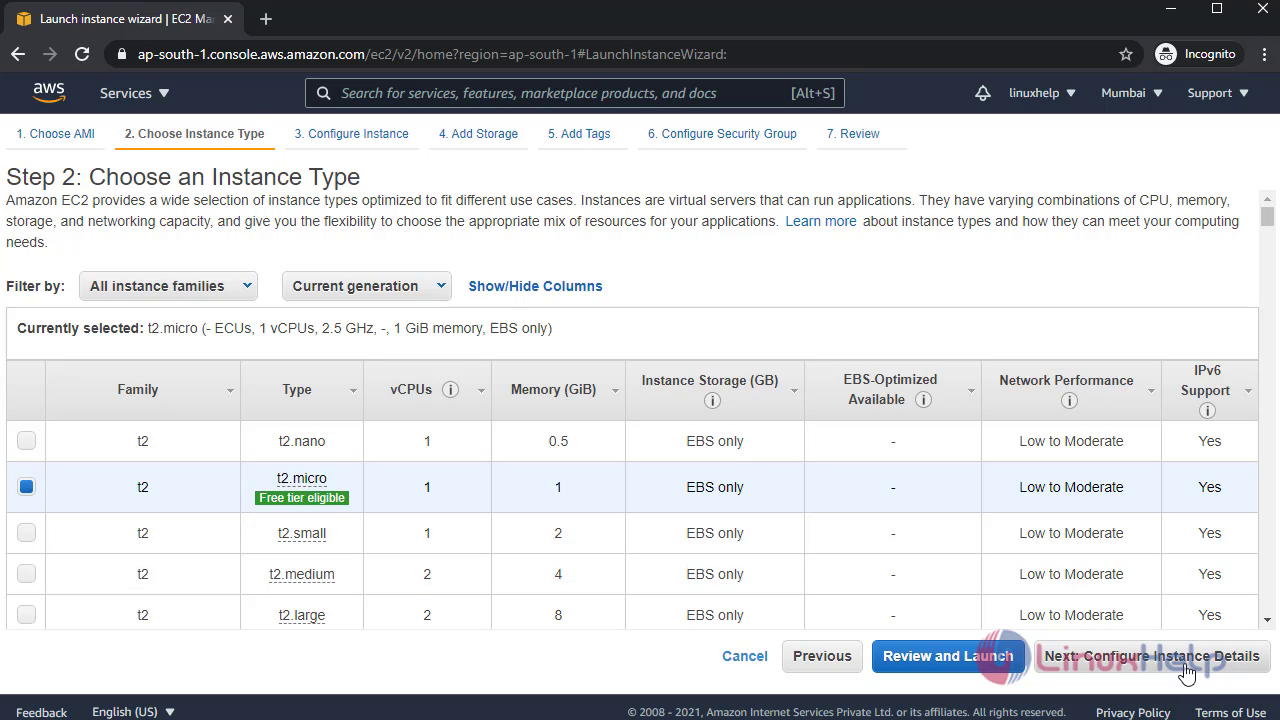
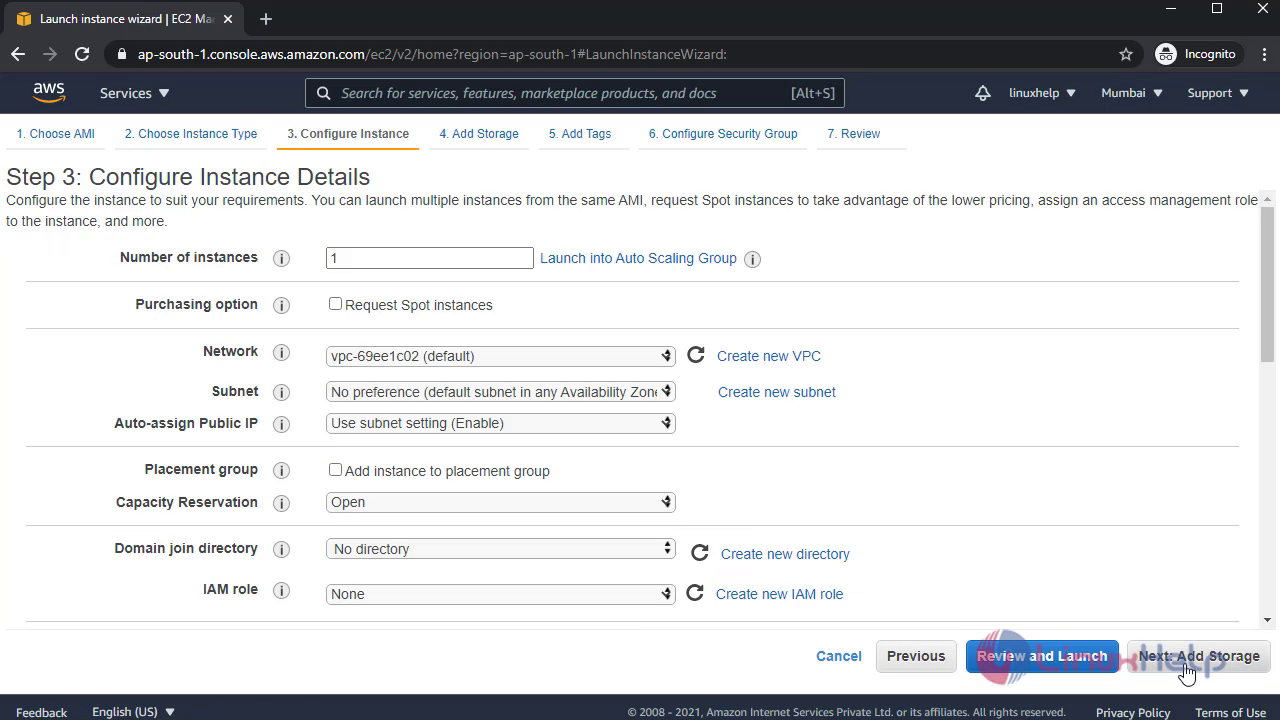
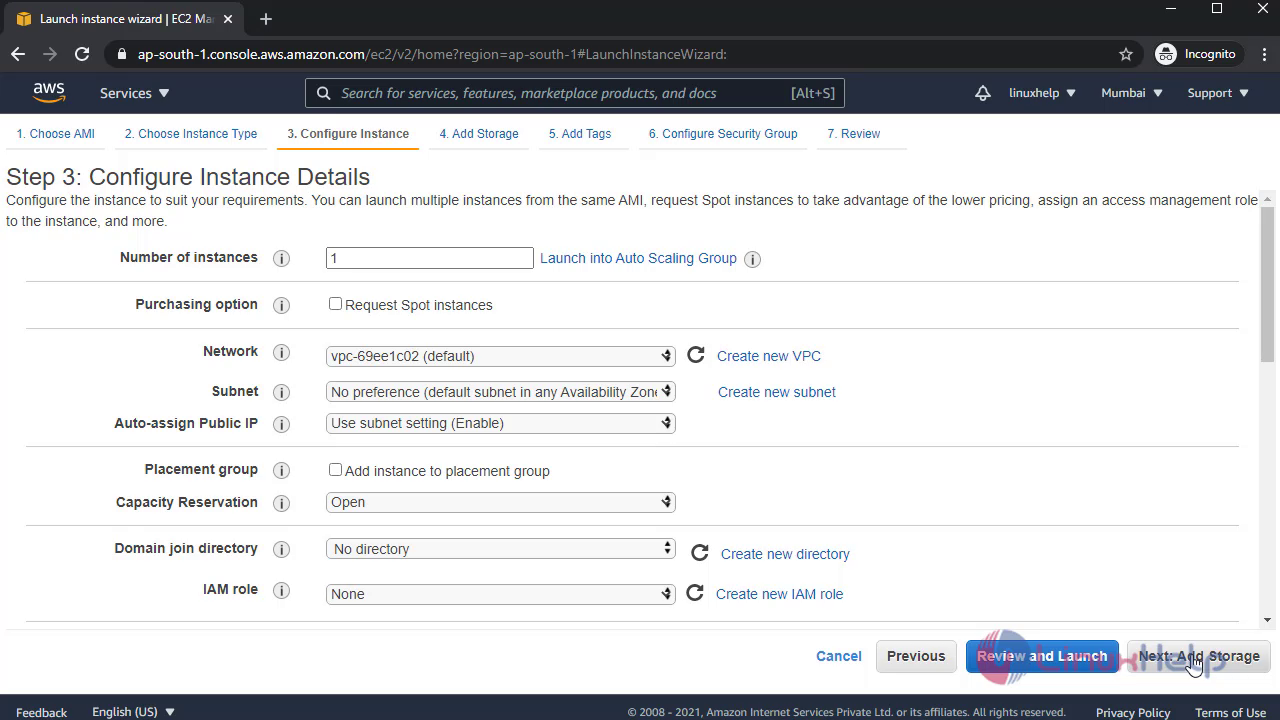
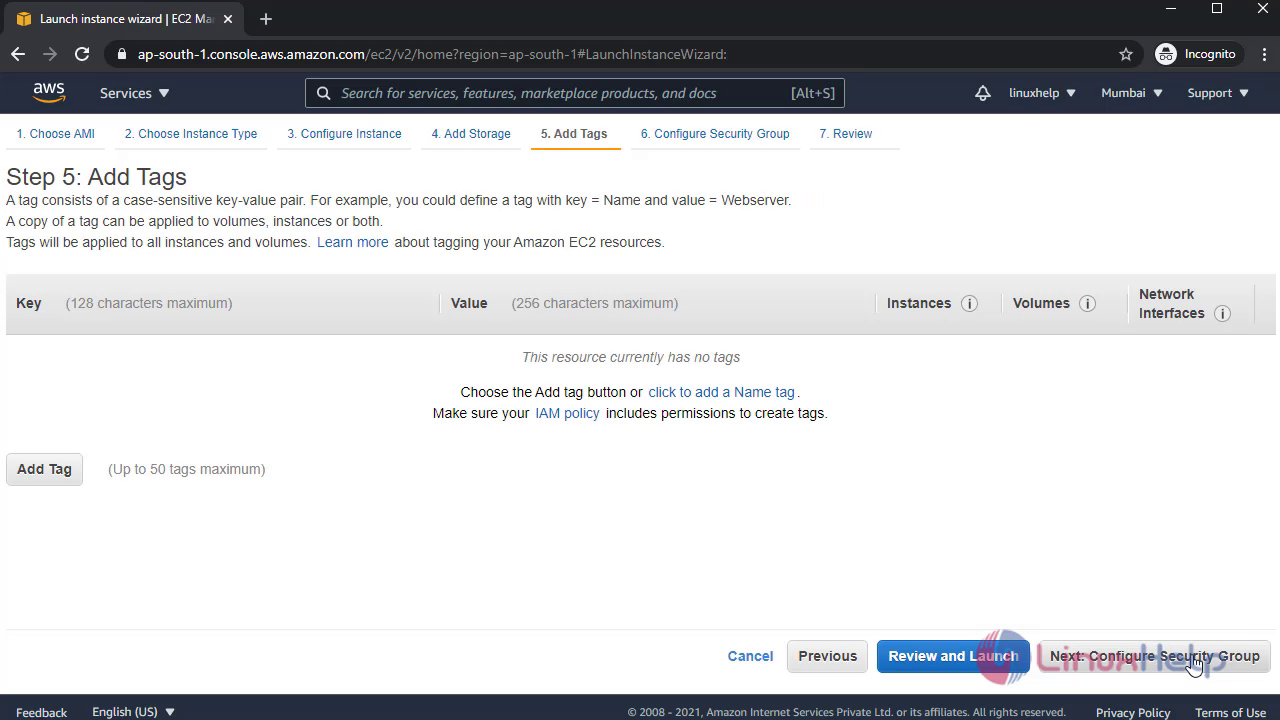
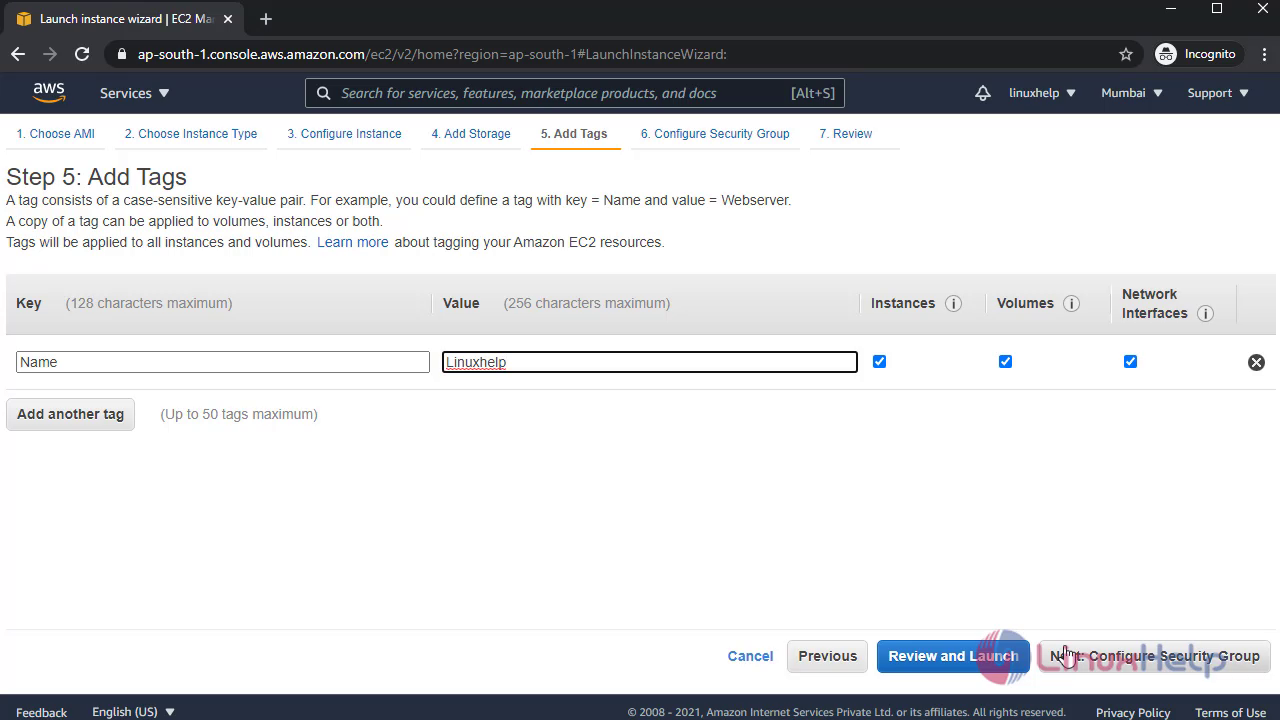
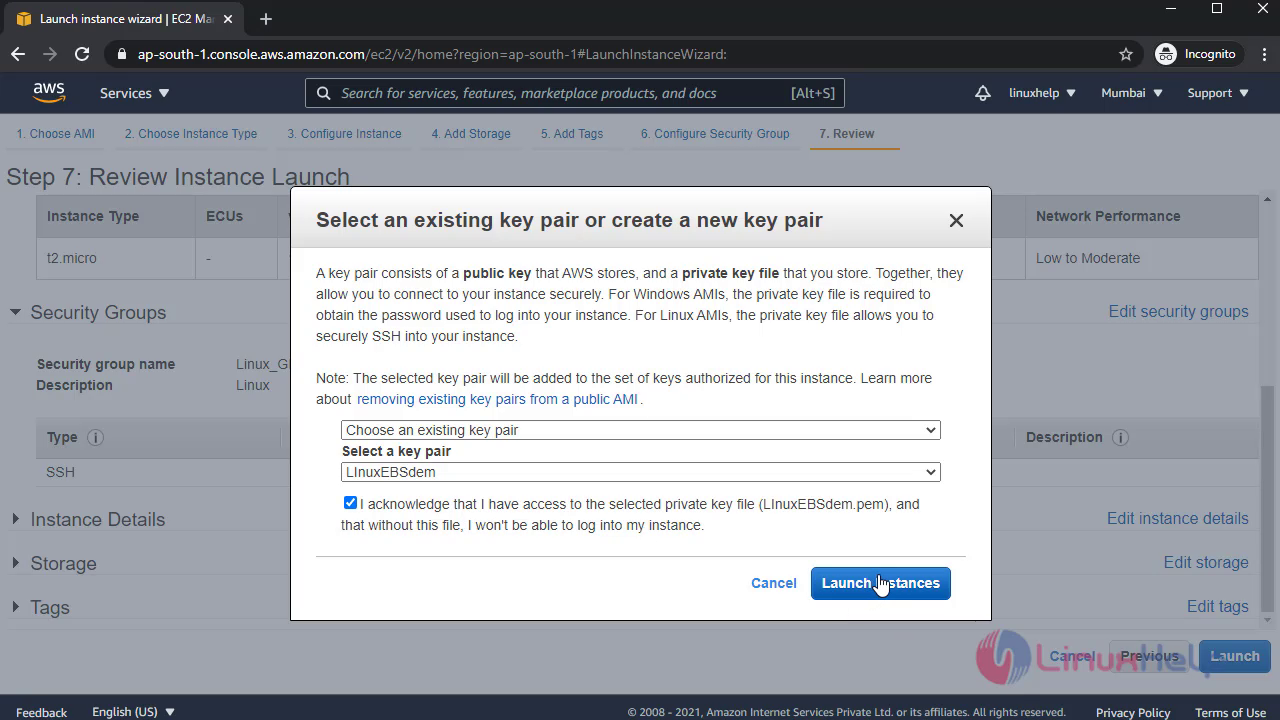
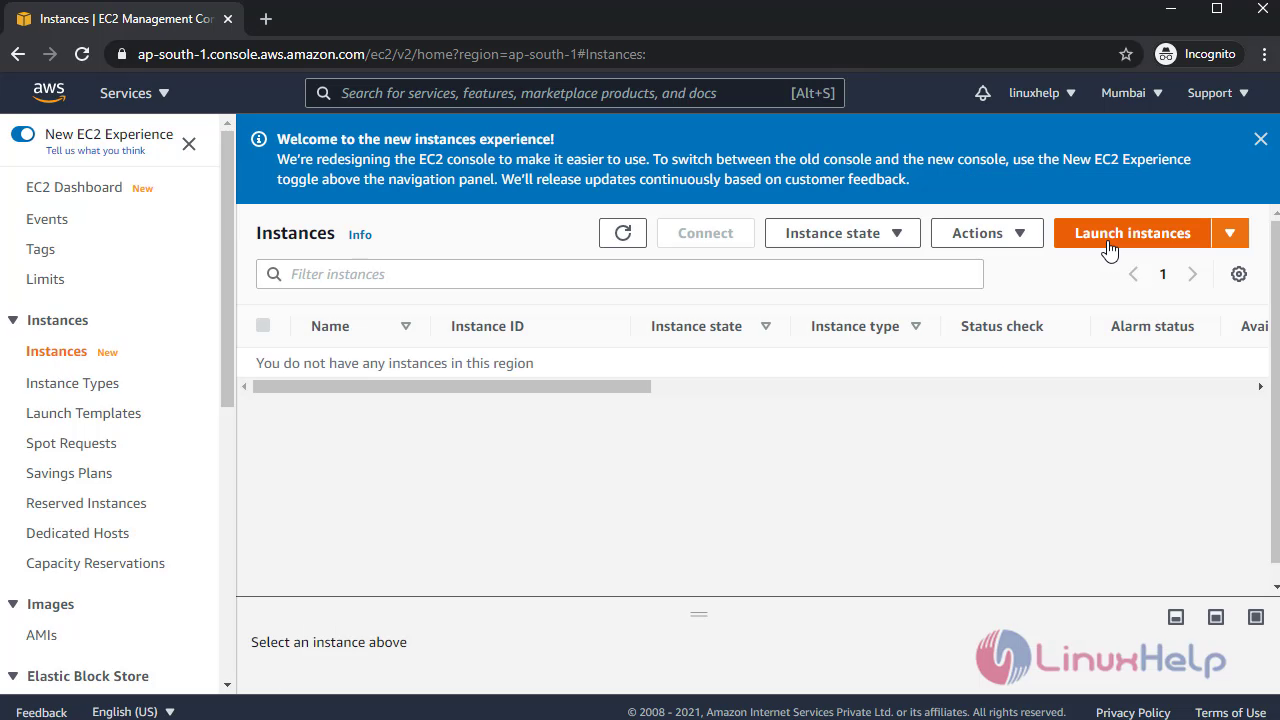 Continue the following steps to launch Instances:
Continue the following steps to launch Instances:
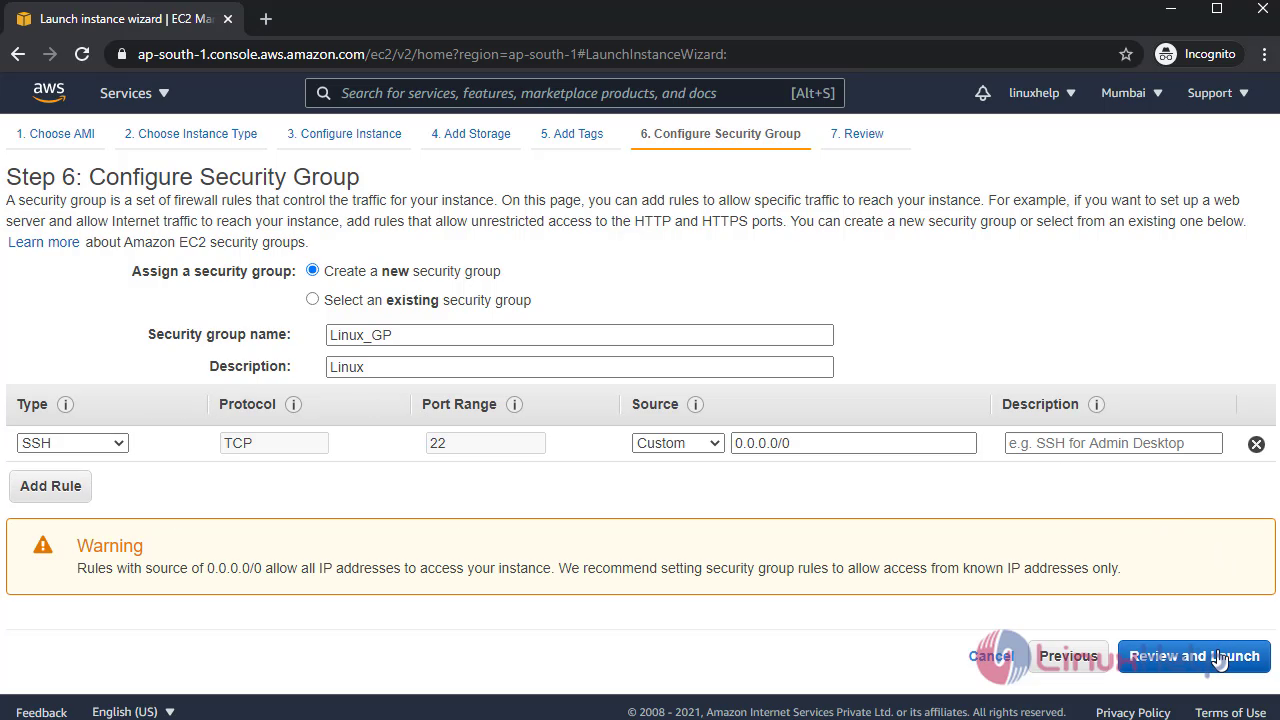
 Create a new security group:
Create a new security group:
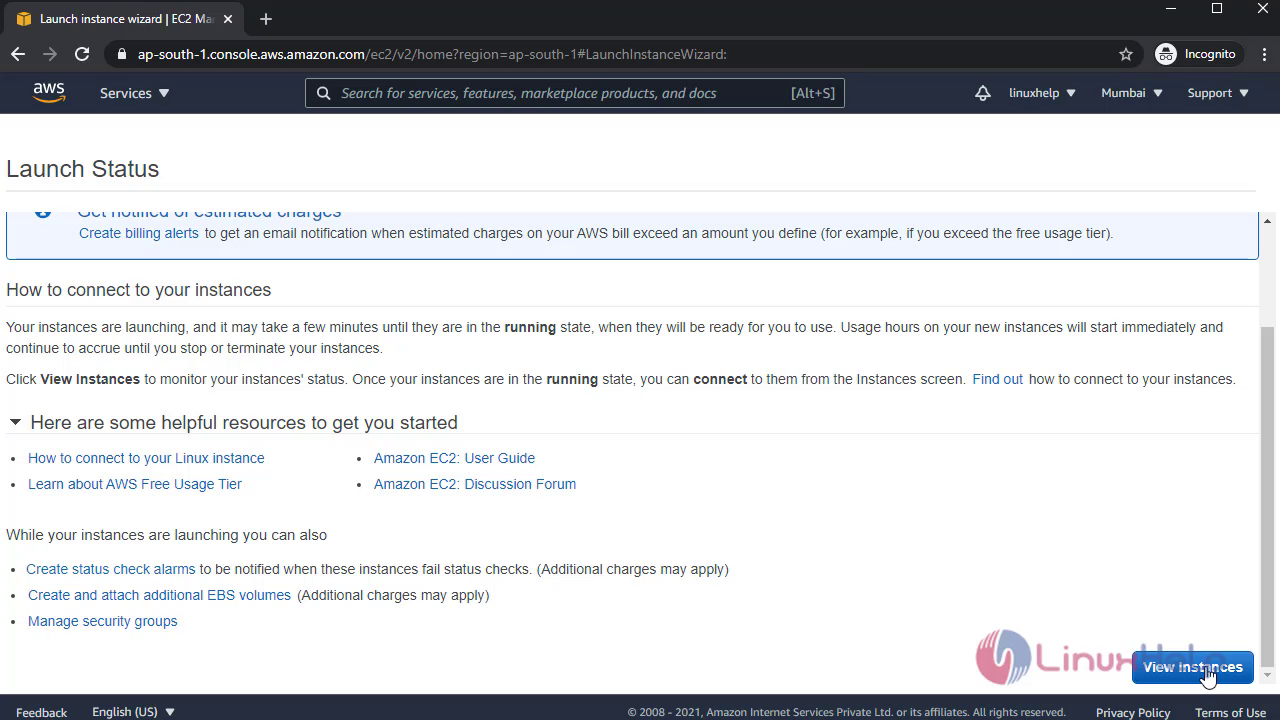
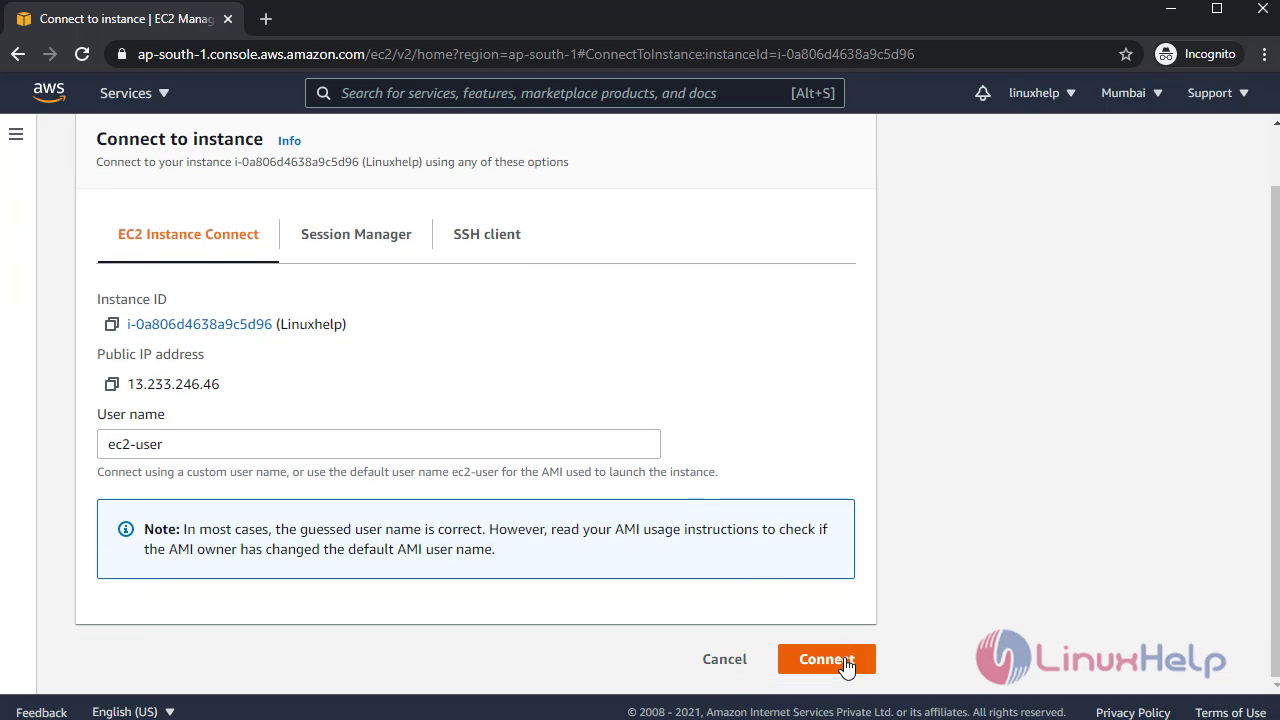
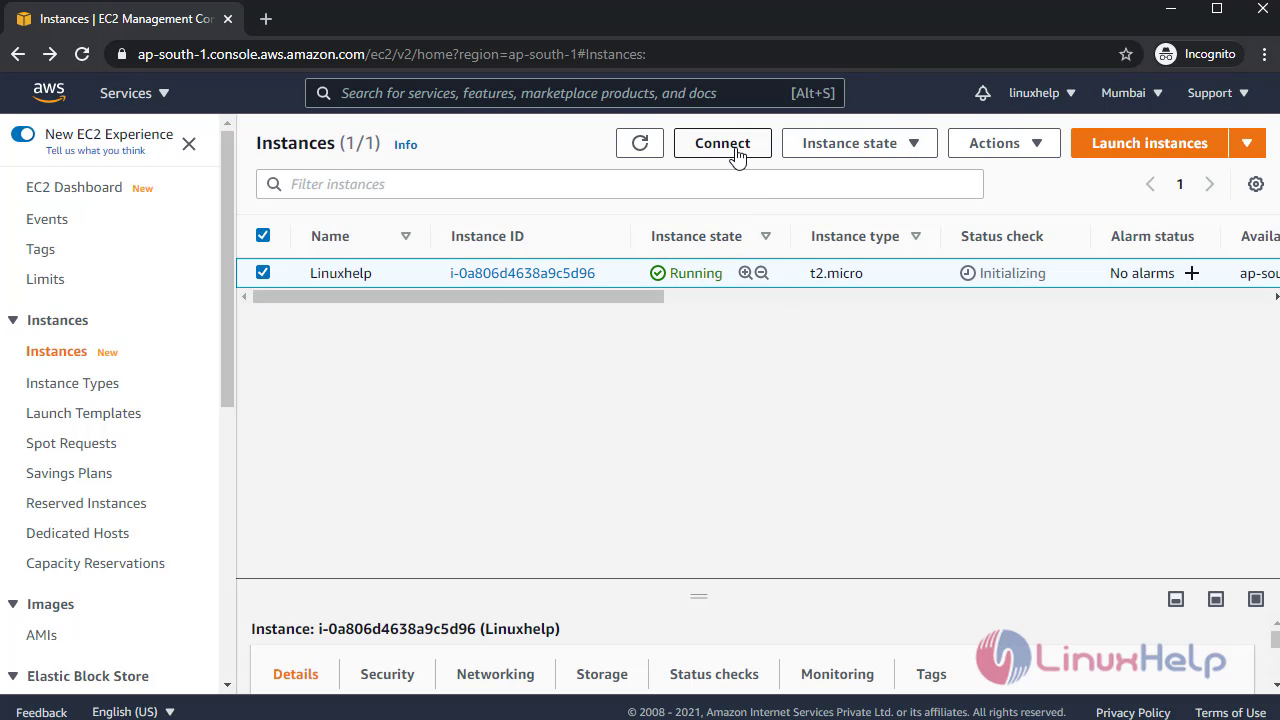 Once completed connect to Instance:
Once completed connect to Instance:
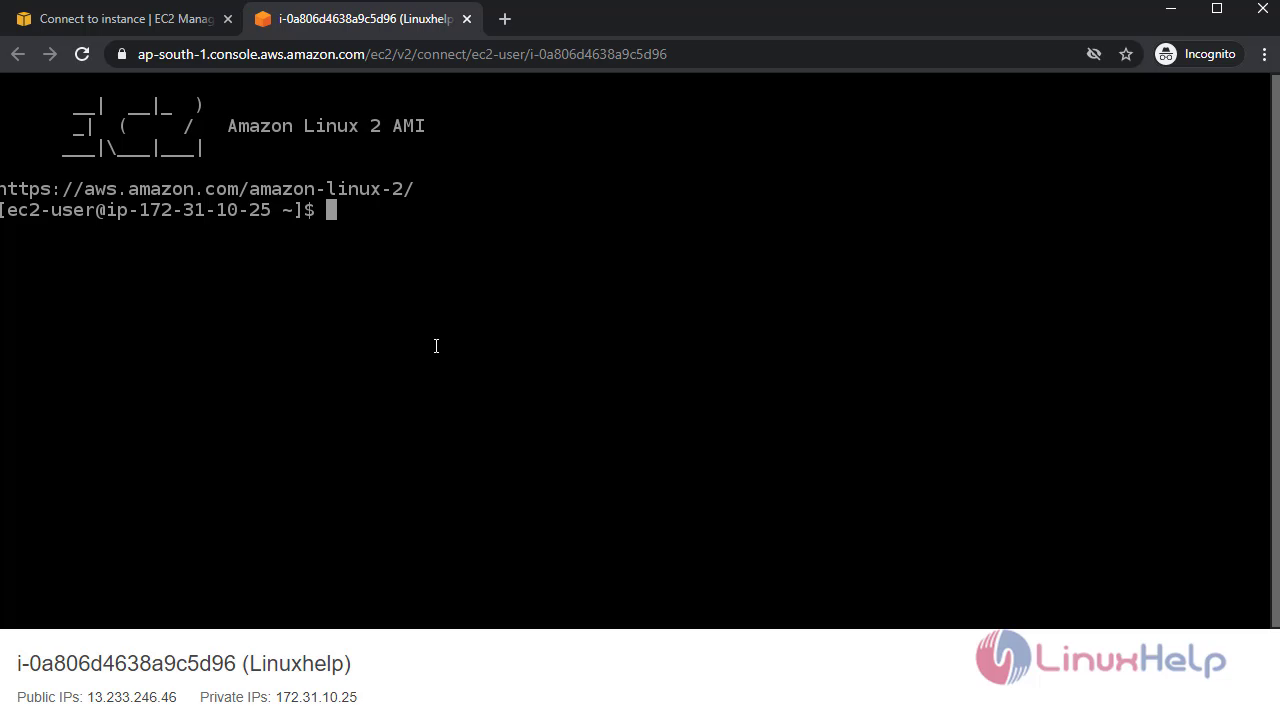
 It will open the Linux terminal:
It will open the Linux terminal:
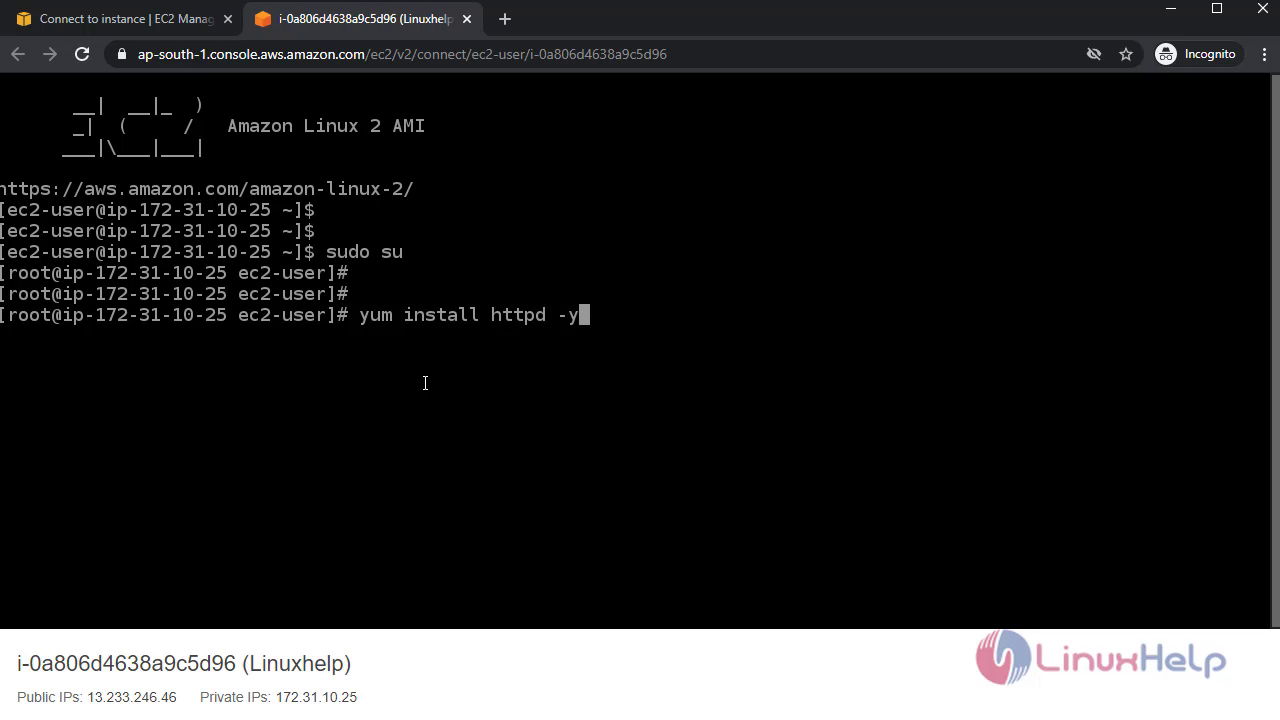
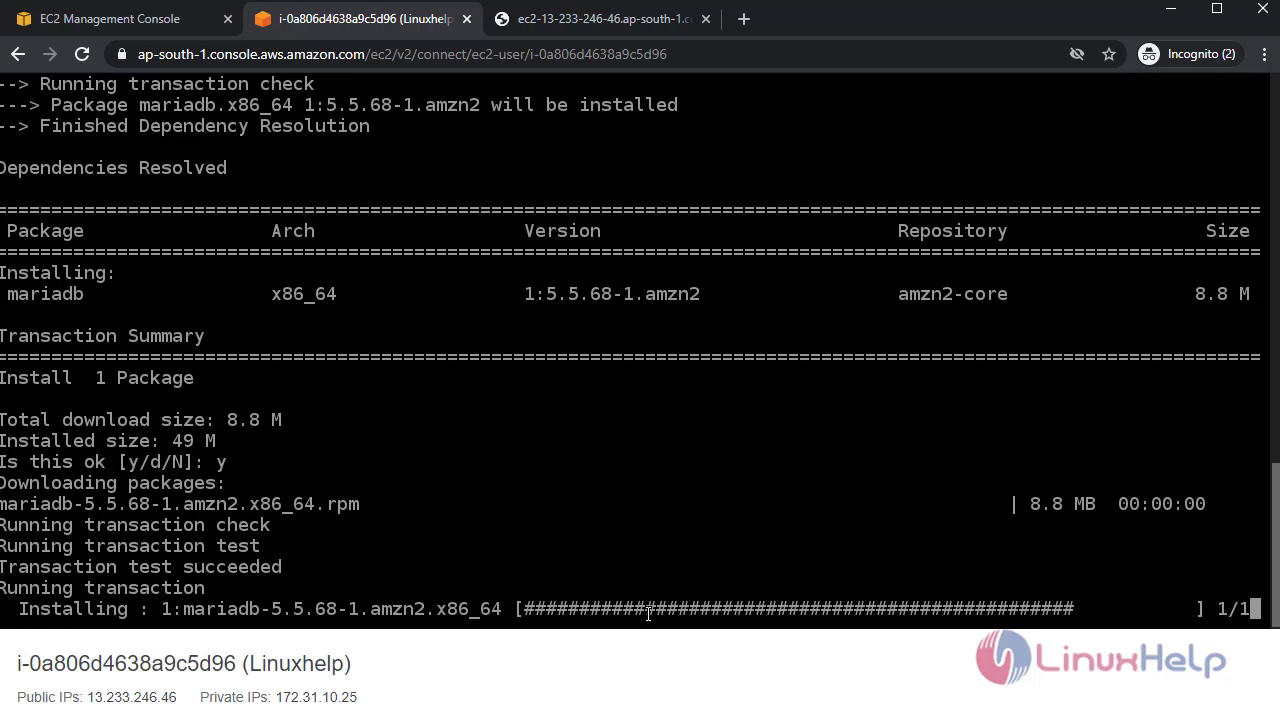
 Install httpd web server:
Install httpd web server:
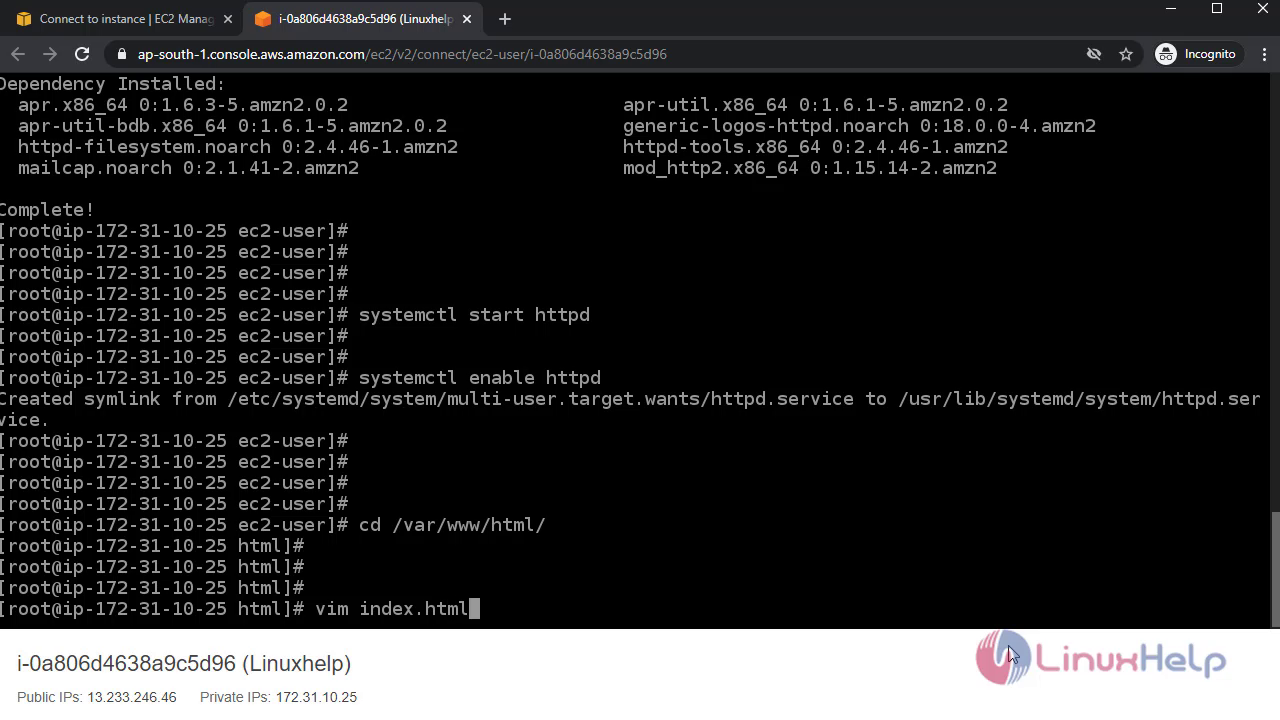
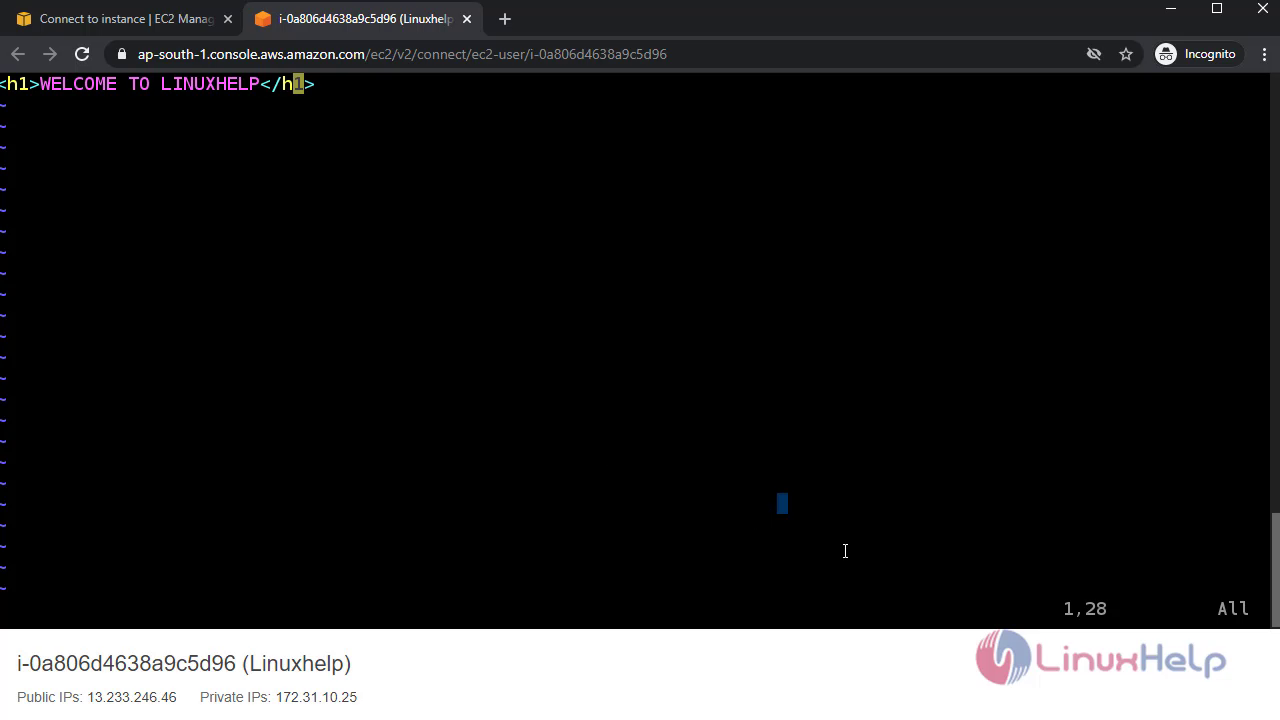
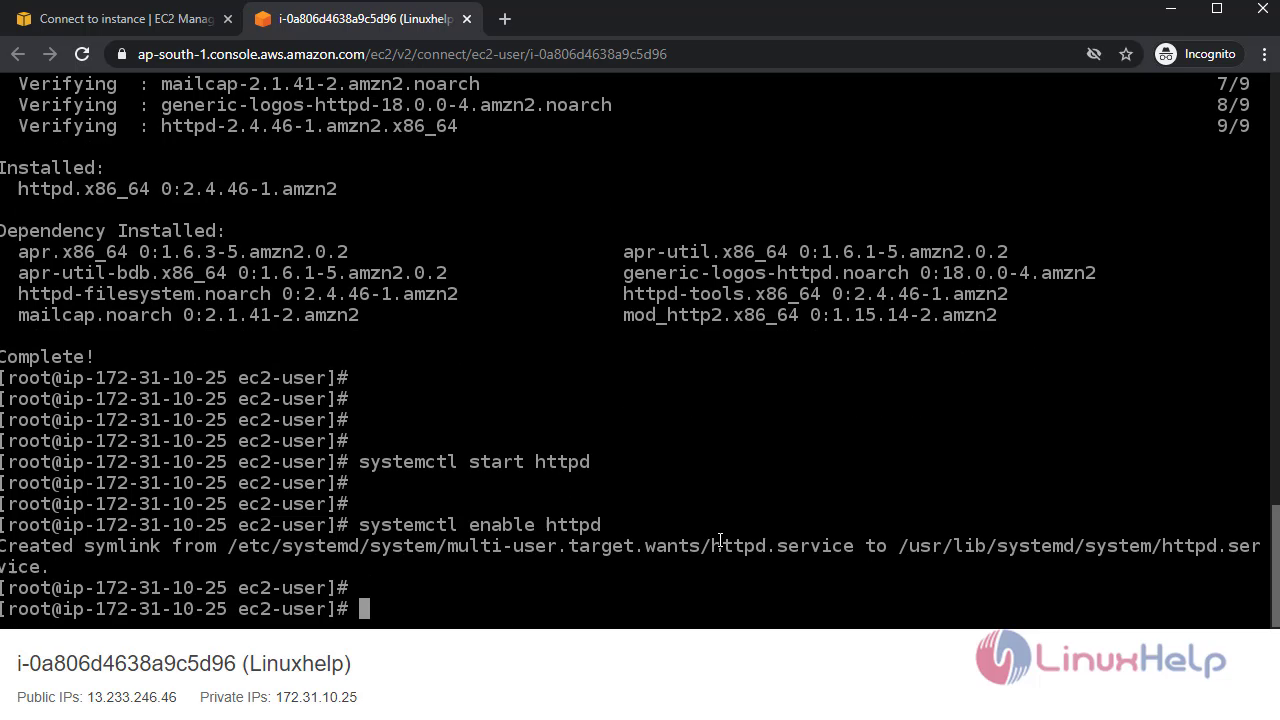 Create a html file:
Create a html file:
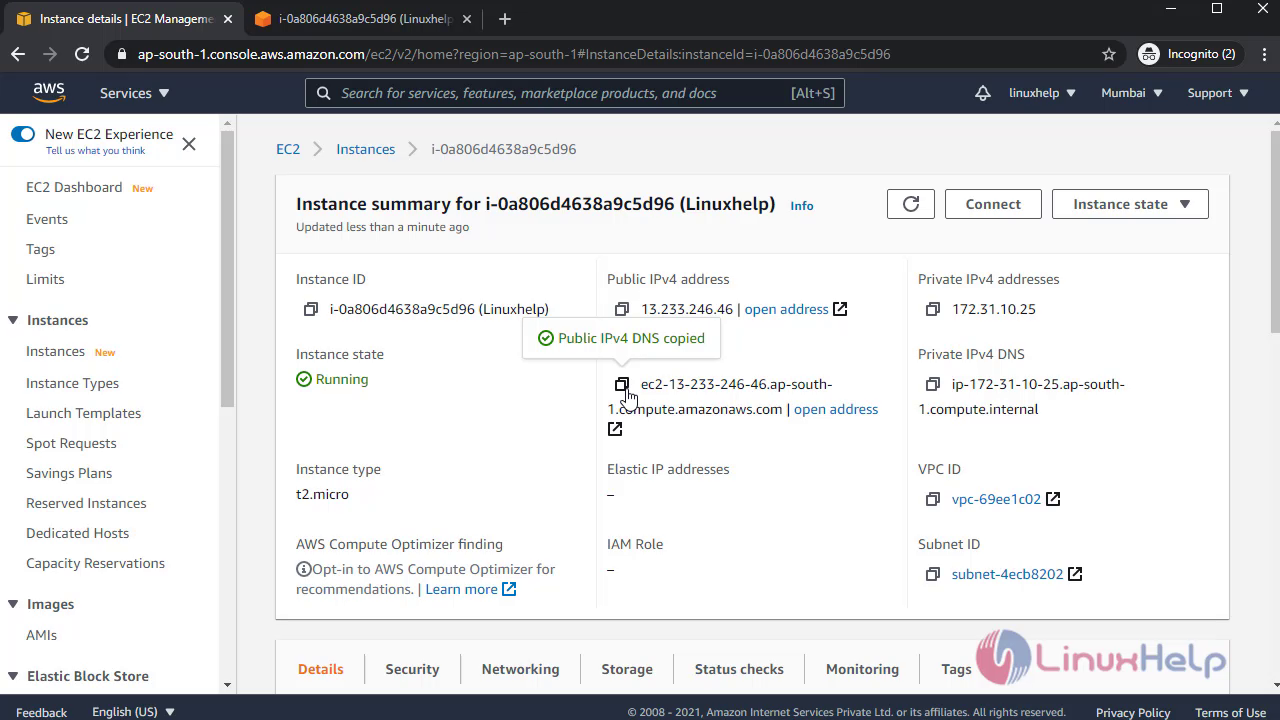
 Once completed go to Instances and copy the Instance Public Ip link:
Once completed go to Instances and copy the Instance Public Ip link:
 Open the link in browser:
Open the link in browser:
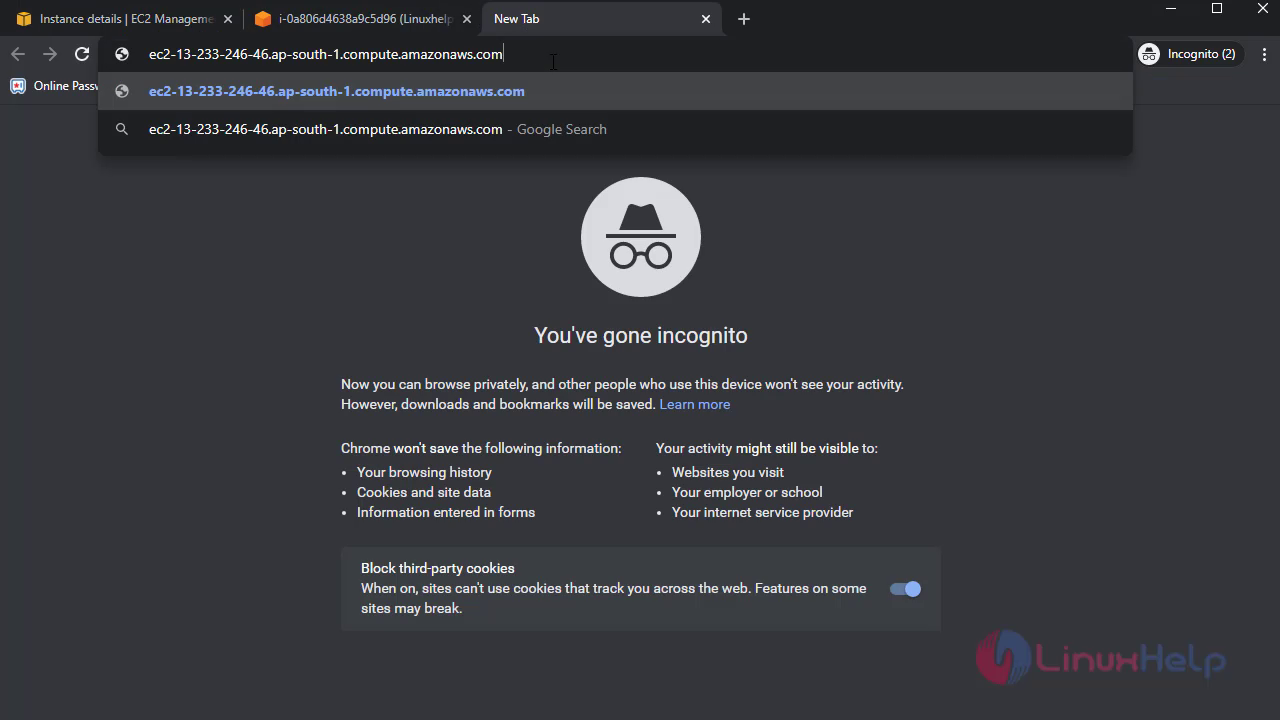 It will not show the content:
It will not show the content:
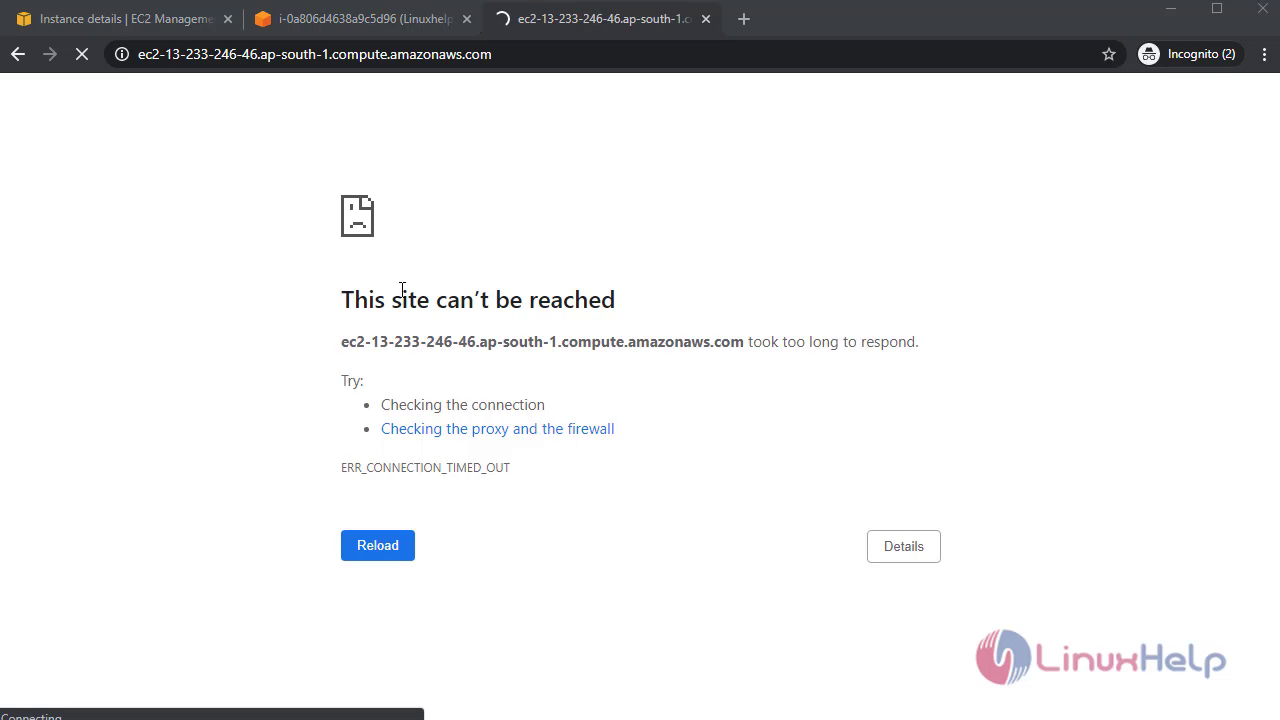 Next, need to give Inbound and Outbound rues:
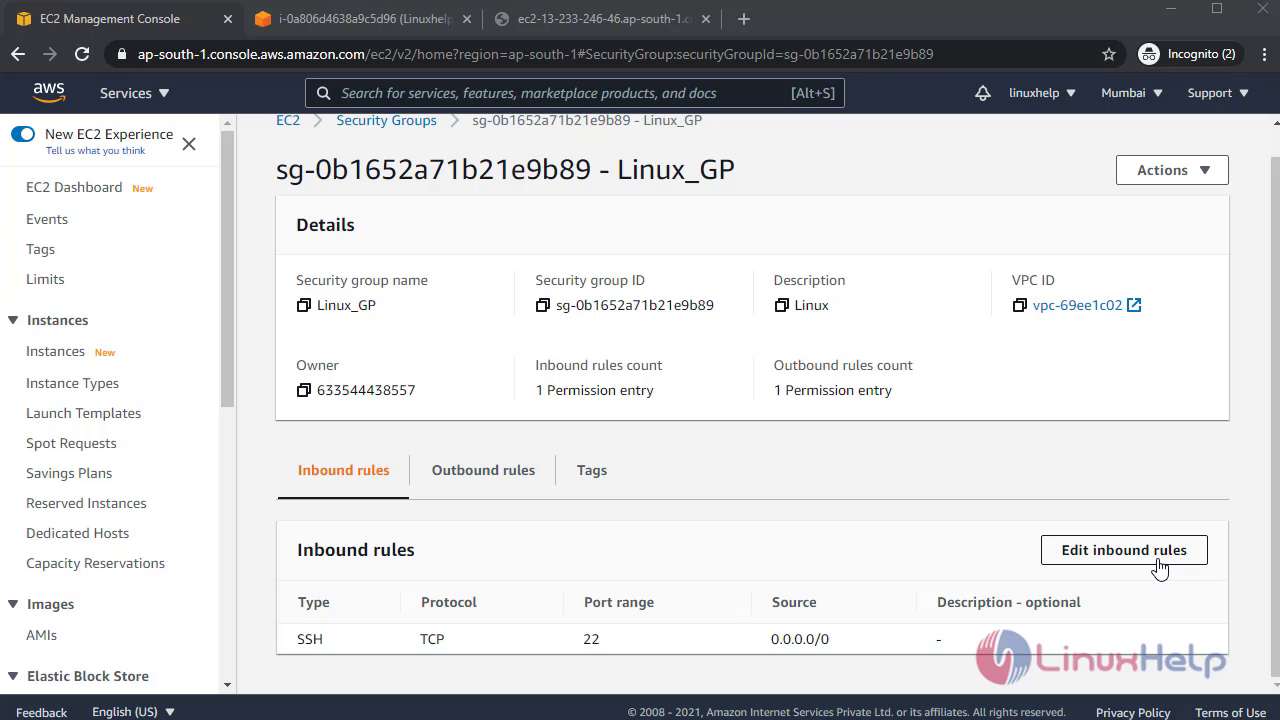
Go to Security:
Next, need to give Inbound and Outbound rues:
Go to Security:
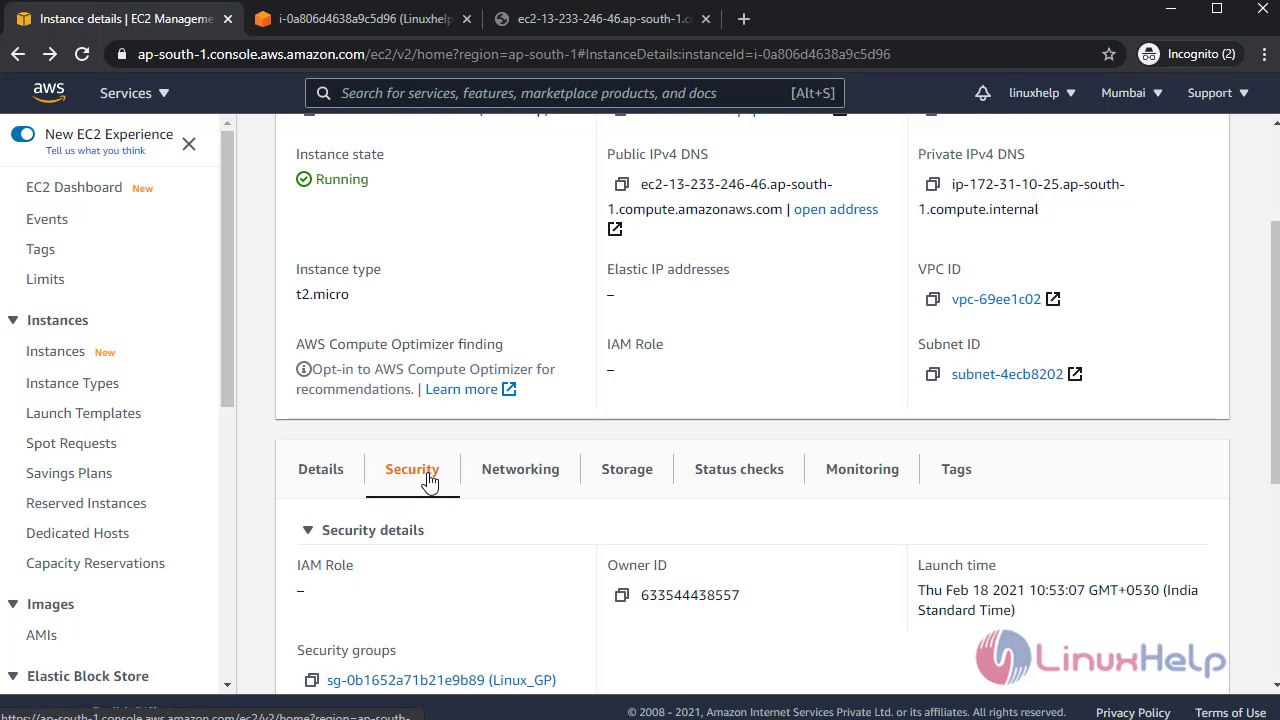
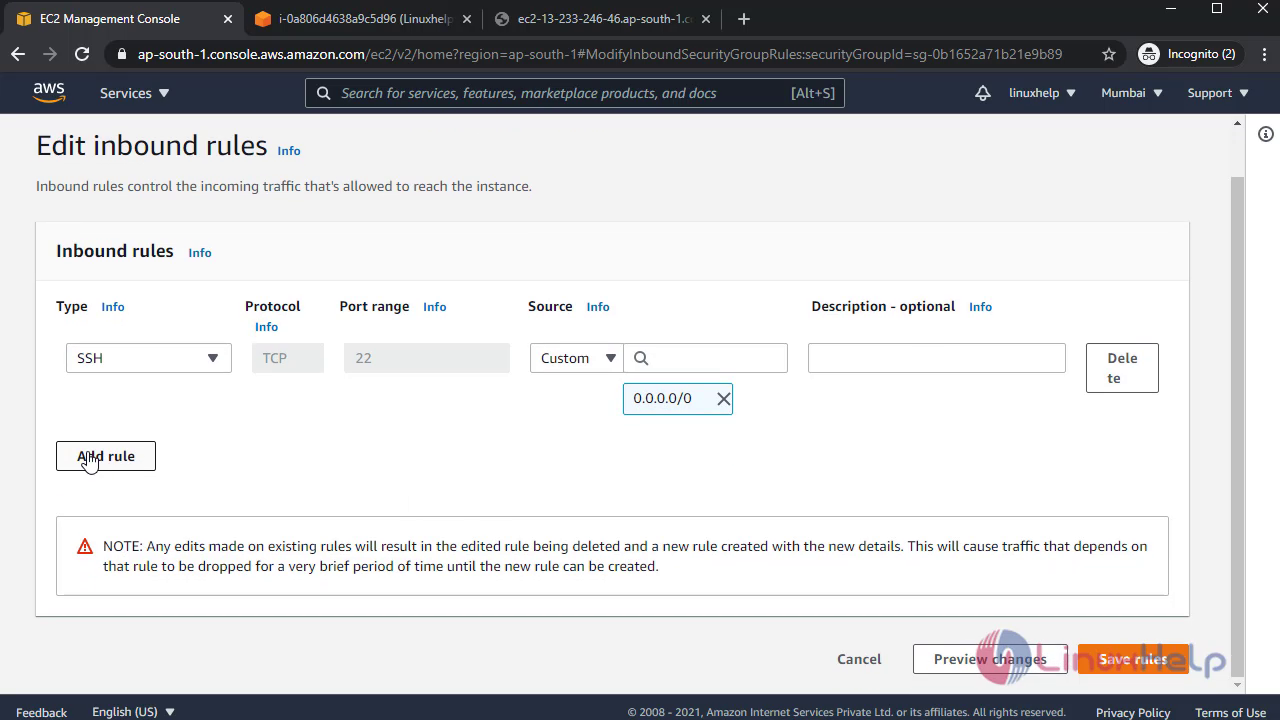
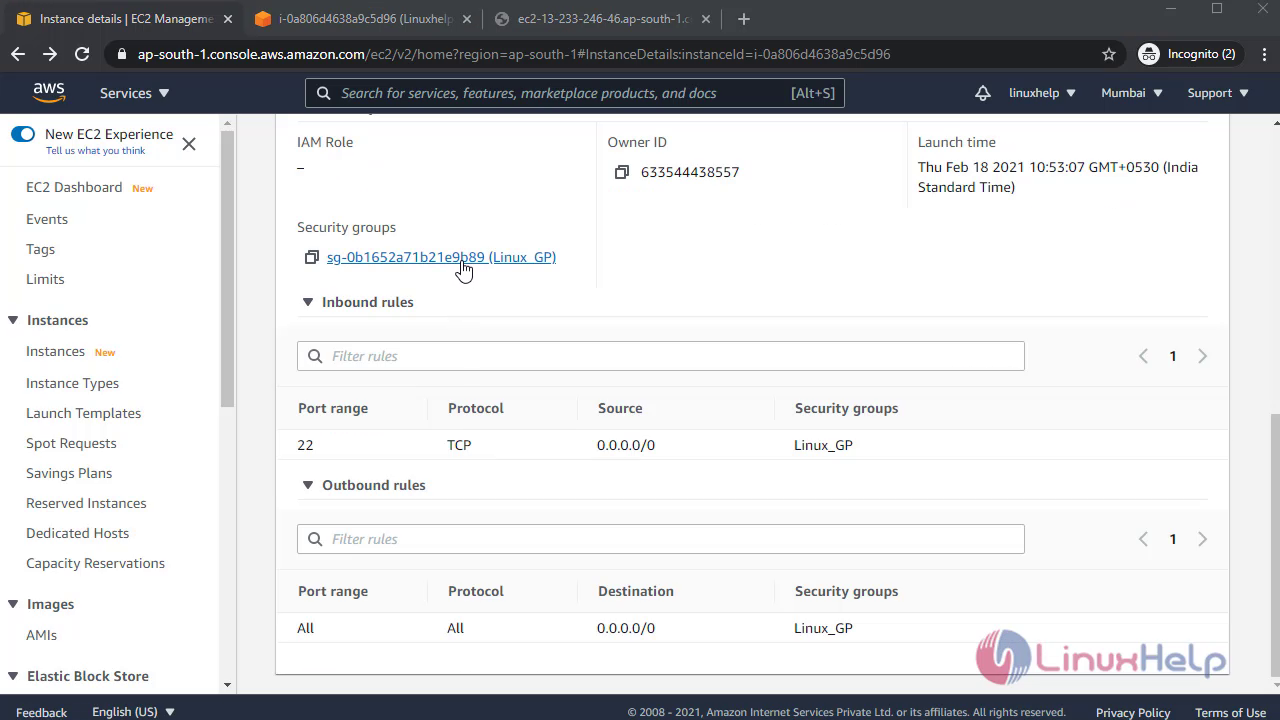 Edit the Inbound rules:
Edit the Inbound rules:
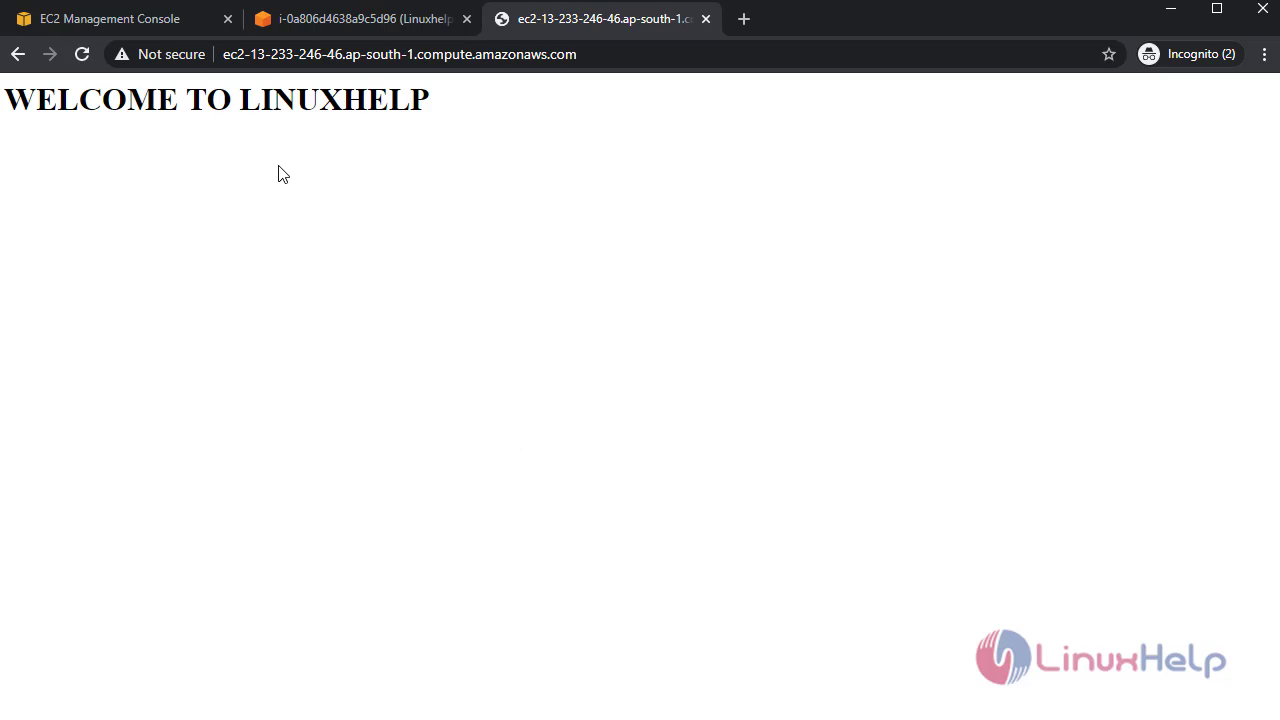
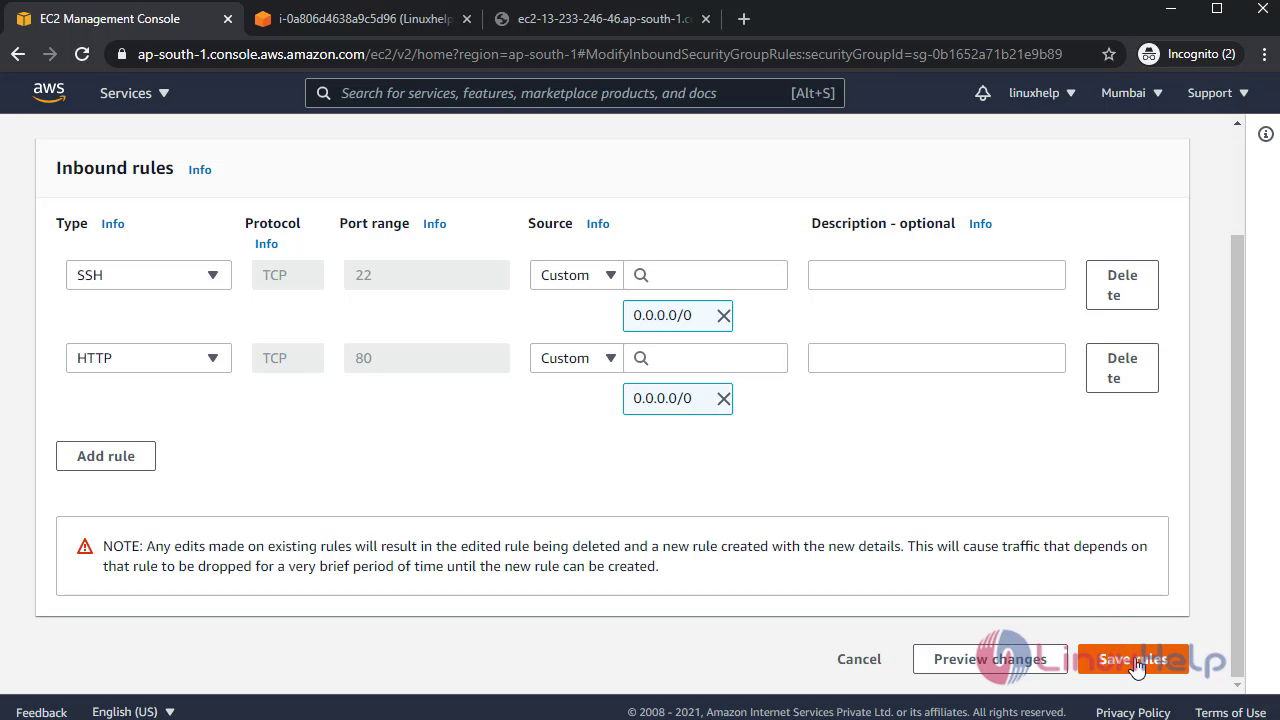 After that reload the browser It will show the content of the Instance:
After that reload the browser It will show the content of the Instance:
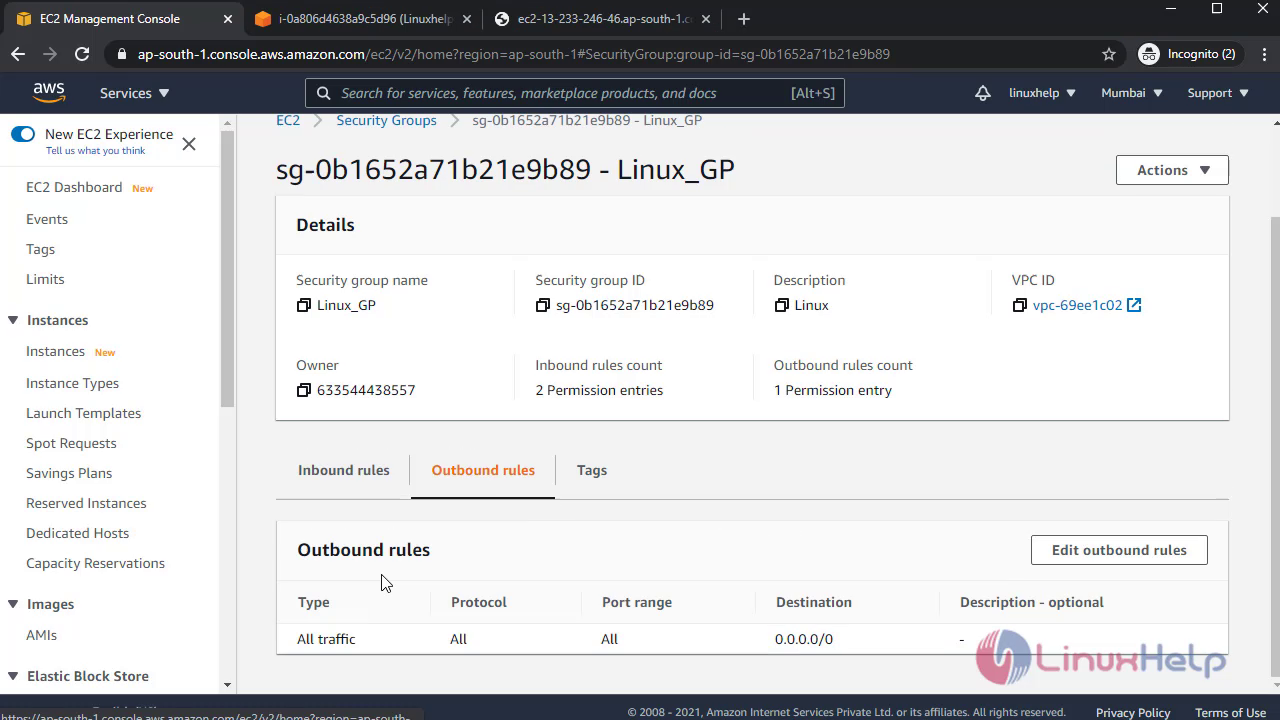
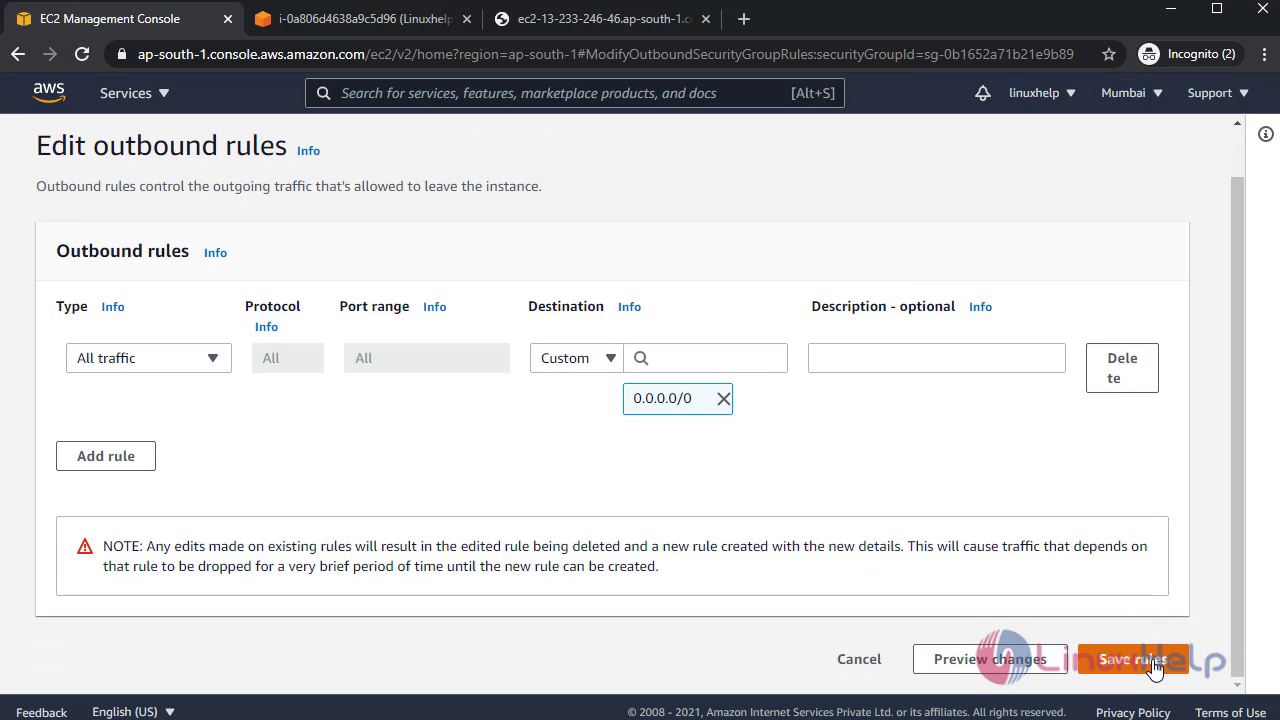
 Edit the Outbound rules:
Edit the Outbound rules:
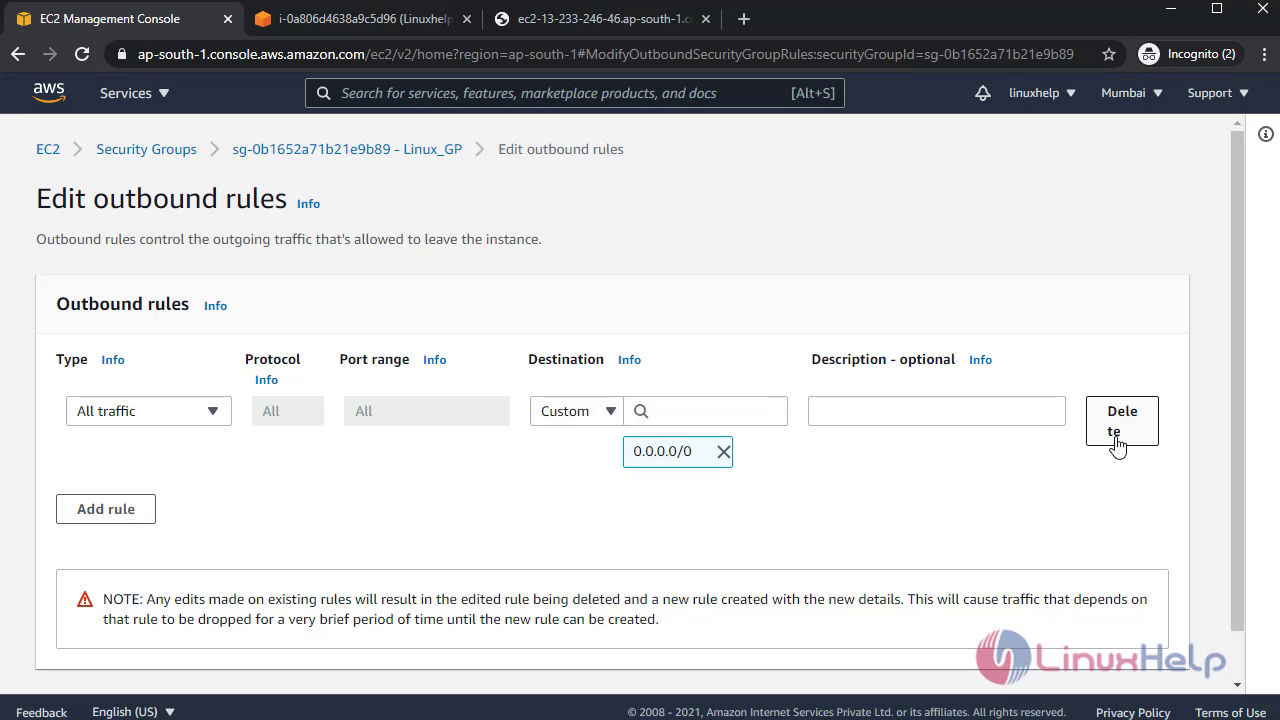
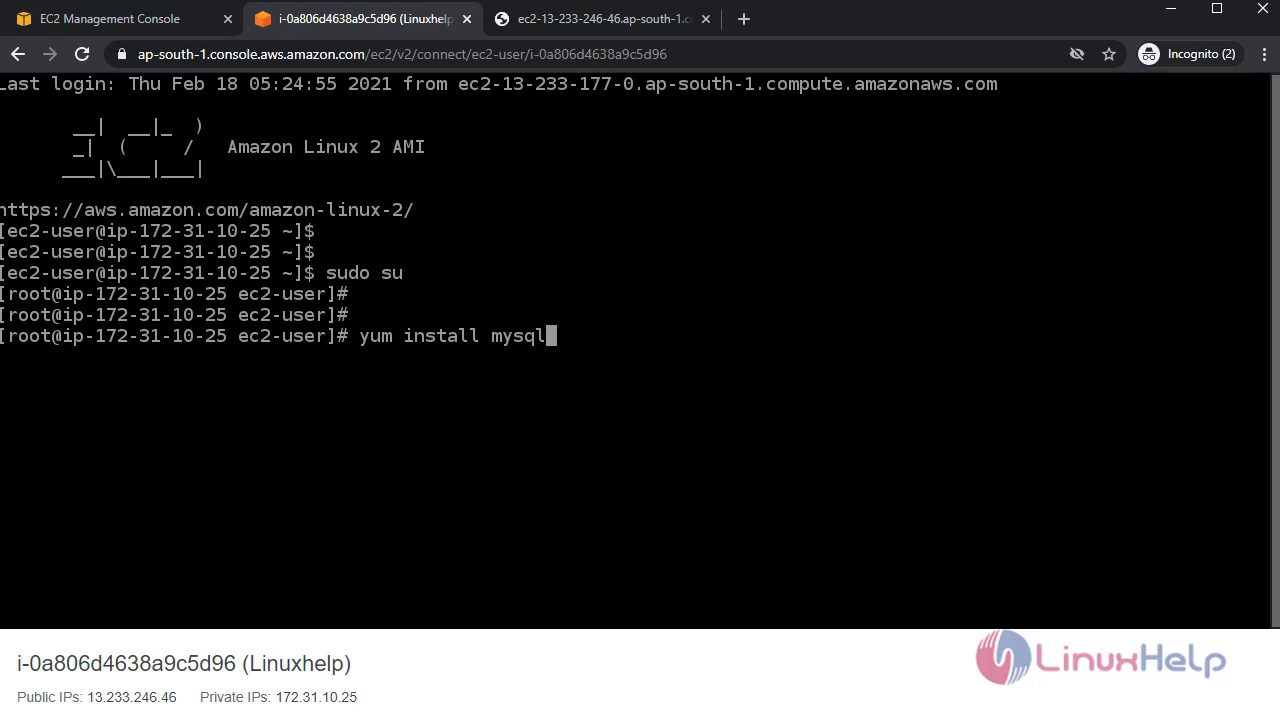
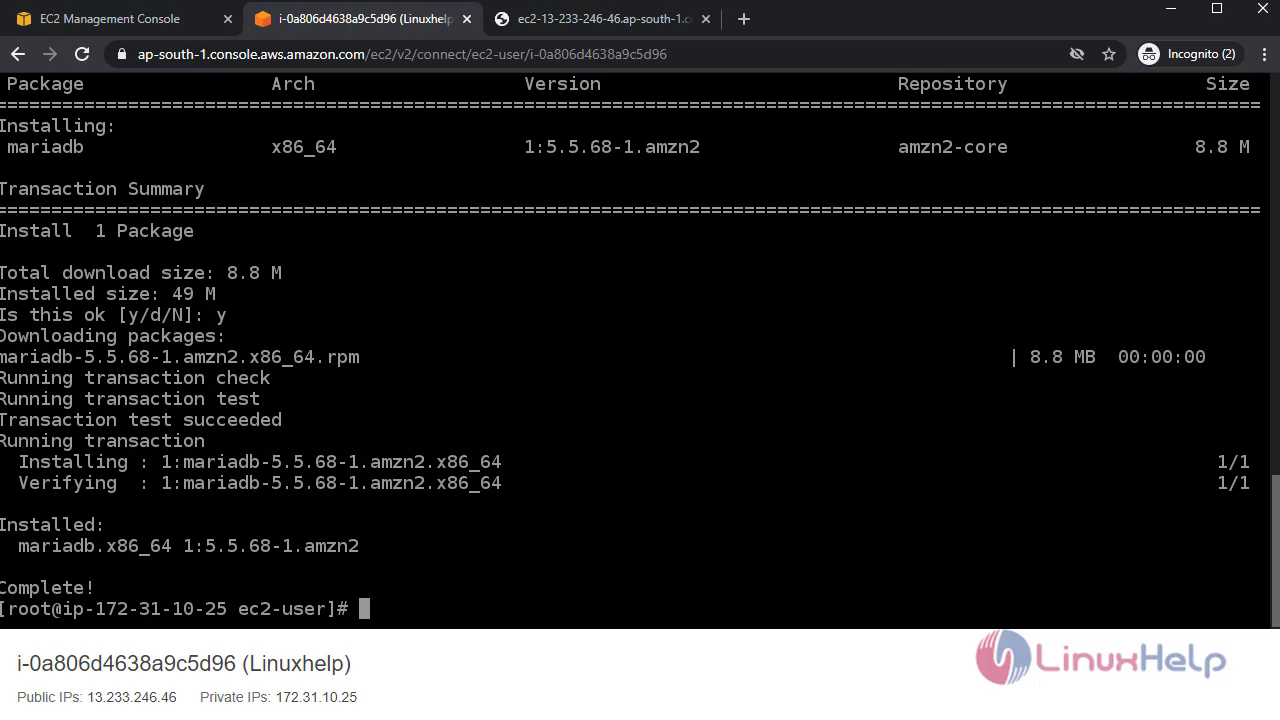
 Now, delete the default Outbound rule and check in terminal:
Now, delete the default Outbound rule and check in terminal:
It will show the mirror error:
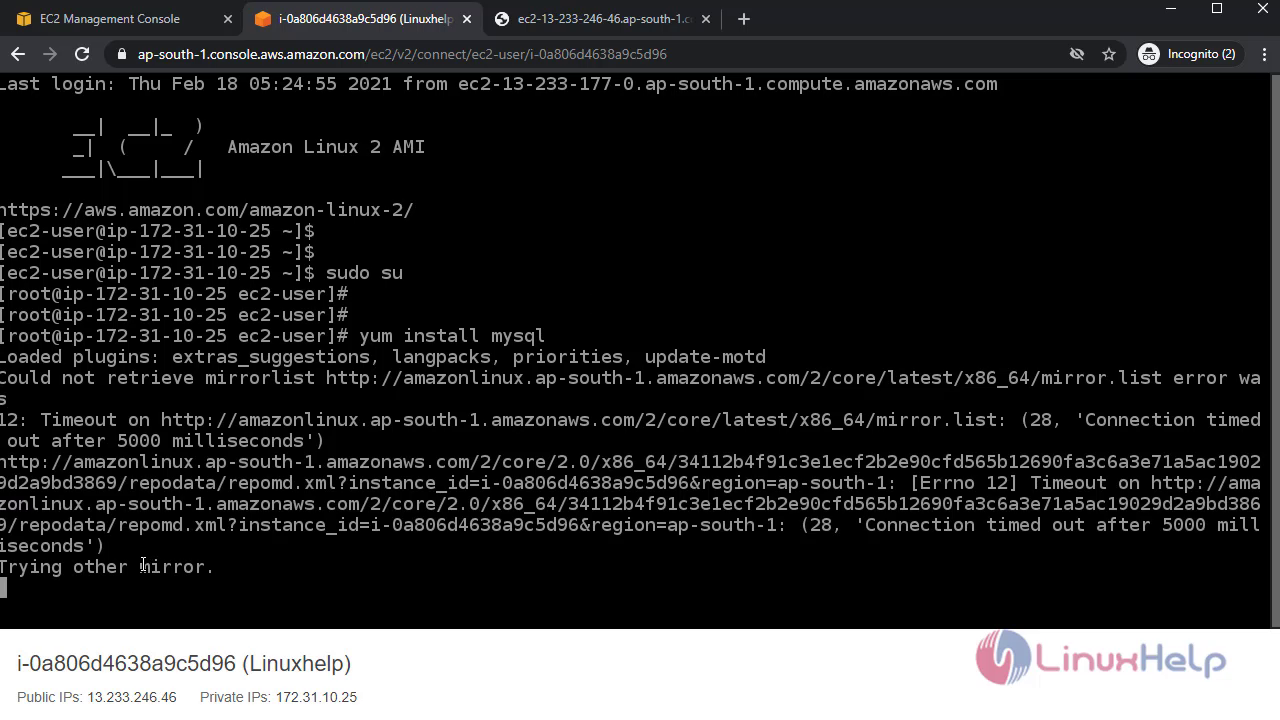 Then, again add the Outbound rule and check:
Then, again add the Outbound rule and check:
 With this method creation of security group with Inbound & Outbound rules in AWS EC2 Instance comes to an end.
With this method creation of security group with Inbound & Outbound rules in AWS EC2 Instance comes to an end.
Comments ( 0 )
No comments available